Amazon Fire 7 2019 (amazon-mustang)
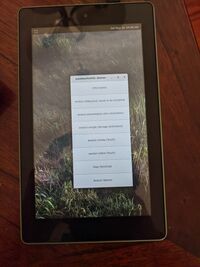 Amazon Fire 7 showing the weston demo UI | |
| Manufacturer | Amazon |
|---|---|
| Name | Fire 7 (2019) |
| Codename | amazon-mustang |
| Released | 2019 |
| Hardware | |
| Chipset | MediaTek MT8163V/B (64-bit quad-core) |
| CPU | 4x 1.3 GHz Cortex-A53 |
| GPU | Mali-T720 MP2 |
| Display | 600x1024 IPS |
| Storage | 16 GB |
| Memory | 1 GB |
| Architecture | armv7 |
| Software | |
| Original software | Android 7.1.1 (Fire OS 6) |
| postmarketOS | |
| Category | testing |
| Pre-built images | no |
| postmarketOS kernel | 4.9.77 |
| Flashing |
Partial |
|---|---|
| USB Networking |
No data |
| Internal storage |
No data |
| SD card |
No data |
| Battery |
No data |
| Screen |
Works |
| Touchscreen |
Works |
| Multimedia | |
| 3D Acceleration |
No data |
| Audio |
No data |
| Camera |
No data |
| Camera Flash |
No data |
| Connectivity | |
| WiFi |
No data |
| Bluetooth |
No data |
| GPS |
No data |
| NFC |
No data |
| Modem | |
| Calls |
No data |
| SMS |
No data |
| Mobile data |
No data |
| Miscellaneous | |
| FDE |
No data |
| USB OTG |
No data |
| HDMI/DP |
No data |
| Sensors | |
| Accelerometer |
No data |
| Magnetometer |
No data |
| Ambient Light |
No data |
| Proximity |
No data |
| Hall Effect |
No data |
| Haptics |
No data |
| Barometer |
No data |
Contributors
- NoriTech
Maintainer(s)
- NoriTech
Users owning this device
- BlackEyedSquid (Notes: 16GB, amonet exploit)
- NoriTech (Notes: ported)
- ThatGeekZen
How to unlock bootloader
The bootloader can now be through a hardware method: https://forum.xda-developers.com/amazon-fire/orig-development/fire-7-2019-mustang-unbrick-downgrade-t3944365
How to enter flash mode
Press and hold +
Installation
Due to the fact that fastboot doesn't work even after using the amonet exploit, you will need to export the boot image and flash it with twrp. Then flash this dummy zip which will force twrp to reapply the amonet exploit.
Another option is exporting a flashable zip that can be flashed using twrp. Refer to Installation Guide for postmarketOS
Amonet
Amonet is lk exploit used to boot unsigend kernel. Sources of amonet are avalible here: https://github.com/xyzz/amonet/tree/mustang. This exploit is installed by bootrom exploit. But probably some 2nd stage bootloader is good idea.
Mainlining
There is some work on mt8163 mainline, for amazon-karnak, but it will be easy to get it on mustang. For now serial console and simplefb is working. Pwrap and pmic seems to be working. https://github.com/mt8163-mainline/linux
Device problems
1. Mainline is not yet usable. 2. Panfrost (driver for mali-t720) is wip, and not avalible in downstream (Merged in linux 5.2) 3. This device use exploit due to locked bootloader. See #Amonet. 4. This device's bl is not very good for running linux, due to it appends much of bad cmdline params, and some things in device tree.
See also
Todo
- pmaports!1263 Initial merge request